Your Road to C|EH MASTER
WHY C|EH MASTER
To be placed at the tip of your organization’s cyber spear, you must be confident, proficient in your job, and be at the top of your game. You must be able to think on your feet, act quickly, appropriately, and proportionally. Make a mistake and bad things can happen.
CEH Master gives you the opportunity to prove to your employer, your peers, and most importantly to yourself that you can in fact take on and overcome challenges found in everyday life as an Ethical Hacker. To prove this, though, we don’t give you exam simulations. We test your abilities with real-world challenges in a realworld environment, and with a time limit, just as you would find in your job.
Do you run towards danger? Do you take charge during unsettling and challenging times? Do you want to be the one your team can rely on to take the fight to the bad guys? If your answers are yes, prove yourself with CEH Master!
WHAT IS C|EH MASTER
CEH Master is the brainchild of our CEO, Jay Bavisi. It is the next evolution for the world-renowned Certified Ethical Hacker program, and a logical ‘next step’ for those holding this prestigious certification. CEH is meant to be the foundation for anyone seeking to be an Ethical Hacker. The CEH Practical Exam was developed to give Ethical Hackers the chance to prove their Ethical Hacking skills and abilities. Earning the CEH Master designation is your way of saying, “I learned it, I know it, I proved it.”
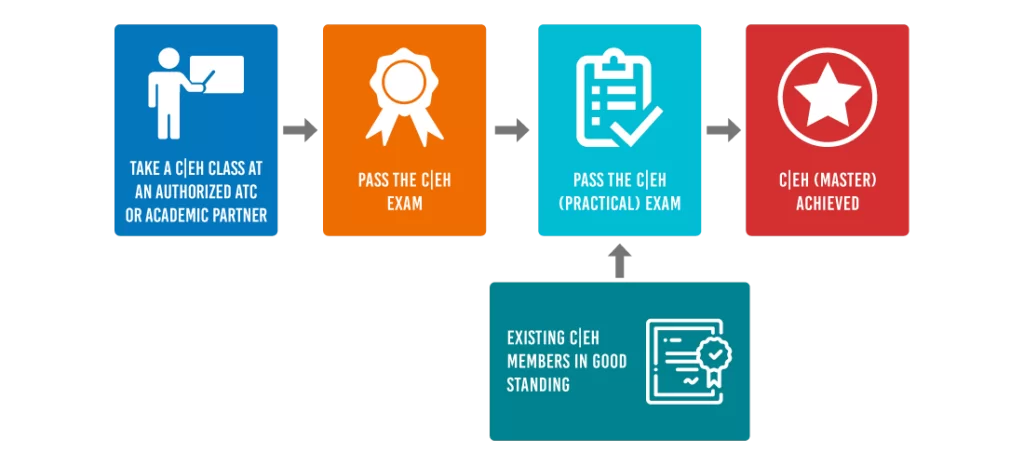
To earn the CEH Master designation you must successfully demonstrate your knowledge of Ethical Hacking through two distinctly different proving grounds. First, you must attempt and successfully pass the ANSI Accredited Certified Ethical Hacker (CEH) multiple choice exam. Once you complete this first step, you can move on to the second part of earning the CEH Master designation, the CEH Practical Exam.
How to attain the C|EH (Master) Credential?
C|EH Master, is the next evolution for the world-renowned Certified Ethical Hacker credential, and a logical ‘next step’ for those holding the prestigious certification. Earning the C|EH Master designation is your way of saying, “I learned it, I understood it, and I proved it.”
About the Exam
Exam#1
C|EH Exam
- Number of Questions: 125
- Test Duration: 4 Hours
- Test Format: Multiple Choice
- Test Delivery: ECC EXAM, VUE
- Exam Prefix: 312-50 (ECC EXAM), 312-50 (VUE)
Exam#2
C|EH (Practical)
- Exam Title: Certified Ethical Hacker (Practical)
- Number of Practical Challenges: 20
- Duration: 6 hours
- Availability: Aspen – iLabs
- Test Format: iLabs Cyber Range
- Passing Score: 70%
- Open Book: Just Like In The Real World!
To prove that you are skills-proficient in Ethical Hacking, we don’t give you exam simulations. Many other certification providers talk about Performance Based Assessments, but the reality is far from them testing your skills on a real-life environment. Most of these ‘performance based tests’ are limited to simulations or interactive ways of theoretically testing your knowledge.
We test your abilities with real-world challenges in a real-world environment, using labs and tools requiring you to complete specific ethical hacking challenges within a time limit, just as you would face in the real world! In the Cybertech Infosolutions C|EH (Practical) exam, a complex network of a large organisation, consisting of various network systems (including DMZ, Firewalls etc.) is replicated, where you as an ethical hacker, have to discover and exploit real time vulnerabilities while also auditing the systems. This is a rare offering, since very few certifications create such environments, while others (including respected brands) only claim to provide hands-on learning and can’t provide experiential learning that’s akin to actually performing the ethical hacking techniques learnt, while working in real life.
ABOUT THE C|EH PRACTICAL
CEH Practical is a six-hour, rigorous exam that requires you to demonstrate the application of Ethical Hacking techniques such as threat vector identification, network scanning, OS detection, vulnerability analysis, system hacking, web app hacking, etc. to solve a security audit challenge.
The hands-on exam will test you to your limits in unearthing vulnerabilities across major operating systems, databases, and networks. It is not a simulated exam. It mimics a real corporate network using live virtual machines, networks, and applications, designed to test your skills. You will be presented with various scenarios and will be asked to demonstrate the application of the knowledge acquired in the CEH course to find solutions to real-life challenges.
Furthermore, you will be given limited time, just like in the real world. The exam was developed by a panel of experienced SMEs and includes 20 real-life scenarios with questions designed to validate essential skills required in the Ethical Hacking domains as outlined in the CEH program
C|EH (PRACTICAL) CREDENTIAL HOLDERS ARE PROVEN TO BE ABLE TO:
- Demonstrate the understanding of attack vectors.
- Perform network scanning to identify live and vulnerable machines in a network.
- Perform OS banner grabbing, service, and user enumeration.
- Perform system hacking, steganography, steganalysis attacks, and cover tracks.
- Identify and use viruses, computer worms, and malware to exploit systems.
- Perform packet sniffing.
- Conduct a variety of web server and web application attacks including directory traversal, parameter tampering, XSS, etc.
- Perform SQL injection attacks.
- Perform different types of cryptography attacks.
- Perform vulnerability analysis to identify security loopholes.
HOW TO PREPARE FOR C|EH (PRACTICAL)
ELIGIBILITY CRITERIA:
There is no predefined eligibility criteria for those interested in attempting the CEH (Practical) exam. However, to earn the CEH Master designation, you must hold both the ANSI Accredited CEH or CEH (Japanese)/CEH(German) certification and the CEH Practical Exam certification.
AGE REQUIREMENT:
The age requirement for attending the training or attempting the exam is restricted to candidates at least 18 years old. Our security experts have designed over 140 labs which mimic real time scenarios in the course to help you “live” through an attack as if it were real and provide you with access to over 2200 commonly used hacking tools to immerse you into the hacker world.
As “a picture tells a thousand words”, our developers have all this and more for you in over 1685 graphically rich, specially designed slides to help you grasp complex security concepts in depth which will be presented to you in a 5 day hands on class by our Certified Cybertech Infosolutions Instructor.
The goal of this course is to help you master an ethical hacking methodology that can be used in a penetration testing or ethical hacking situation. You walk out the door with ethical hacking skills that are highly in demand, as well as the internationally recognized Certified Ethical Hacker certification! This course prepares you for Cybertech Infosolutions Certified Ethical Hacker exam 312-50.
The C|EH (Practical) is a 6 hours practical exam built to exacting specifications by subject matter experts in the Ethical Hacking field. Professionals that possess the C|EH credential are be able to sit for exam that will test their limits in unearthing vulnerabilities across major operating systems, databases, and networks. To those who meet and exceed the skills level set, they will earn the new industry required certification – the C|EH (Practical) certification.
C|EH (Practical) is available only as an online and fully proctored exam because we insist that that is the only way quality can be assured. Cybertech Infosolutions is the first in the world to offer a fully online, remote proctored practical exam in the world!
The overall benefit of a practical exam that is fully proctored anywhere in the world will provide organizations with a skills-validated and trusted credential when employing cybersecurity professionals. With its global availability, organizations can now quickly train, test and deploy a cyber-ready workforce effectively.
The Certified Ethical Hacking training course will significantly benefit security officers, auditors, security professionals, site administrators, and anyone who is concerned about the integrity of the network infrastructure.
Duration: 5 Days (9:00 AM – 5:00 PM)
Eligibility Criteria:
In order to be eligible to attempt Cybertech Infosolutions CEH, certification examination, candidate may opt to:
Attend Official Training:
If a candidate have completed an official Cybertech Infosolutions training either at an Accredited Training Center, via the iClass platform, or at an approved academic institution, the candidate is eligible to attempt the relevant Cybertech Infosolutions exam without going through the application process. For more information click HERE
Attempt Exam without Official Training:
In order to be considered for the Cybertech Infosolutions CEH exam without attending official training, candidate must have at least 2 years of work experience in the Information Security domain and remit a non-refundable eligibility application fee of USD 100.00 along with their application form. For more information click HERE
iLearn (Self-Study)
This solution is an asynchronous, self-study environment which delivers Cybertech Infosolutions’s sought-after Ethical hacking training courses in a streaming video format.
iWeek (Live Online)
This solution is a live, online, instructor-led training course which means you can attend an ethical hacking course with a live instructor from anywhere with an internet connection.
Master Class
This solution offers you the opportunity to learn from world-class instructors and the opportunity to collaborate with top Infosecurity professionals.
Training Partner (In Person)
This solution offers “in-person” ethical hacking training so that you can get the benefit of collaborating with your peers and gaining real-world skills, conveniently located in your backyard.
Module 01: Introduction to Ethical Hacking
Module 02: Footprinting and Reconnaissance
Module 03: Scanning Networks
Module 04: Enumeration
Module 05: Vulnerability Analysis
Module 06: System Hacking
Module 07: Malware Threats
Module 08: Sniffing
Module 09: Social Engineering
Module 10: Denial-of-Service
Module 11: Session Hijacking
Module 12: Evading IDS, Firewalls, and Honeypots
Module 13: Hacking Web Servers
Module 14: Hacking Web Applications
Module 15: SQL Injection
Module 16: Hacking Wireless Networks
Module 17: Hacking Mobile Platforms
Module 18: IoT Hacking
Module 19: Cloud Computing
Module 20: Cryptography

